Executive Summary
- In this article, we’ll put one of the most damaging forms of malware under the microscope: ransomware.
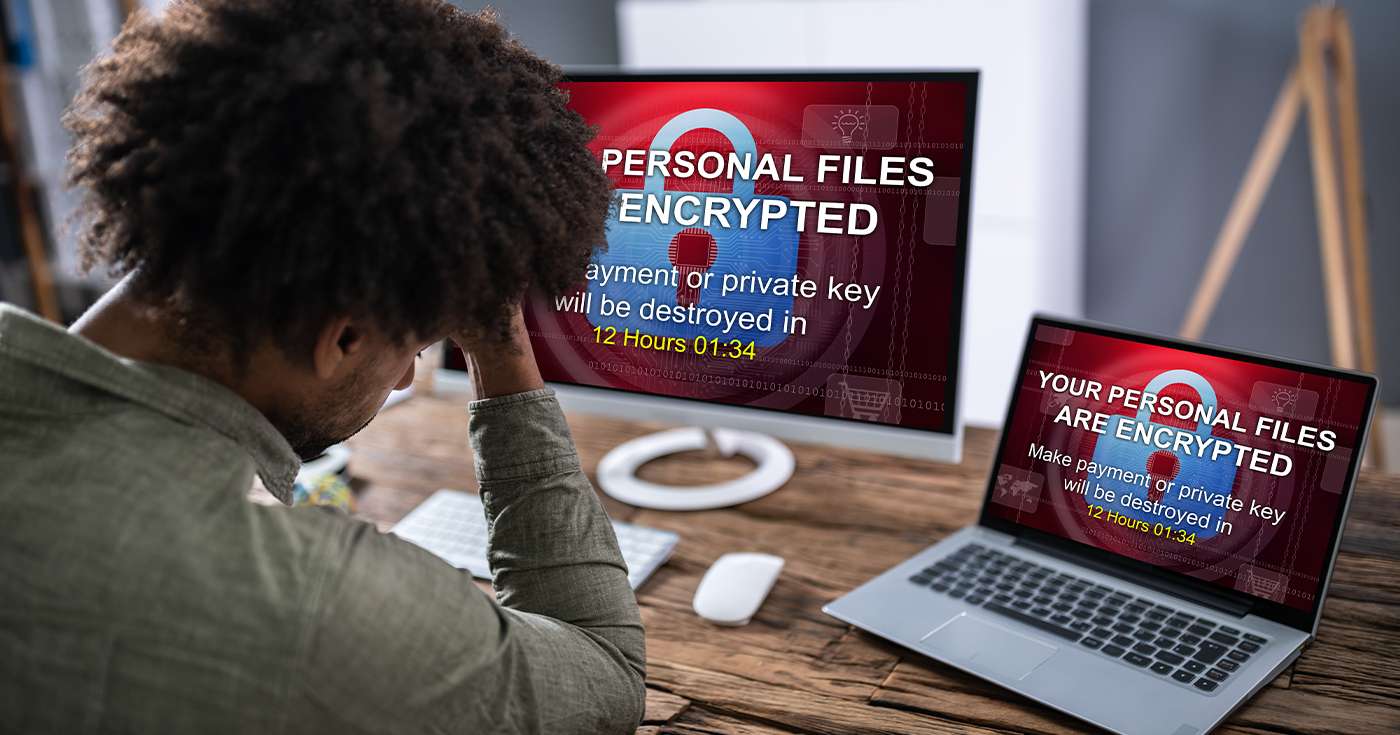
- Just as the name suggests, ransomware is a type of malware attack which aims to encrypt files on a computer then demand payment – usually in the form of cryptocurrency – to unlock them.
Introduction
When it comes to malware, names don’t get much more descriptive than “ransomware”.
A lot of it is spelled out for you right there, but there are still plenty of questions.
What exactly does a cyberattack like this hold to ransom? How do ransomware attacks find their victims? What happens if a business refuses to cough up?
We’ll answer all of these questions – and a few more besides – in this comprehensive article covering one of the most devastating forms of malicious software: ransomware.
What is ransomware?
Ransomware is a type of malware designed to hijack a user’s data – usually by way of encrypting it – unless a ransom is paid to decrypt it.
When a user suffers an encrypting ransomware attack, they may find that they cannot access any of their essential files, such Office documents, images, and other critical data.
Ransomware attacks are actually a form of Trojan horse attack, because they’re commonly delivered to an unsuspecting user’s computer via a file which looks entirely legitimate – perhaps as an email attachment or downloadable file. Once executed on a computer, the trojan horse delivers the payload: a malicious program which immediately sets about encrypting as many files as possible, then shows a pop-up message with details of how and where to pay the ransom.
Encrypting ransomware isn’t the only variant of this attack. Here are a couple of other common types of ransomware:
- Non-encrypting ransomware can take control of a user’s computer in invasive ways, (for example, by randomly showing adult material), and attackers demand payment for a code to stop the behaviour.
- Exfiltration, also known as ‘leakware’, threatens to publish a user’s sensitive documents online unless a ransom is paid.
- Mobile ransomware is becoming more common on Android devices, and usually takes the form of a ‘blocker’ which prevents the user from accessing their apps as normal (until a ransom is paid, of course).
The origins of ransomware
Known by the technical name cryptoviral extortion, (and interestingly inspired by the facehugger creature in the 1979 movie Alien), the world’s first piece of encrypting ransomware came about in 1989.
Known as the Aids Info Disk Trojan, or PC Cyborg Trojan, this attack was created by evolutionary biologist Dr. Joseph Popp. Intriguingly, the payload of the attack was actually delivered via floppy disk. Members of a mailing list, hijacked by Dr Popp, were sent the disk in the mail which, when inserted into the computer, would encrypt important files and – after a certain number of reboots – show a message about their software being out of date and requiring a fee of $189 to renew.
The final surprising twist in this origin story is that Dr Popp defended himself by claiming all of the extorted money was destined for AIDS charities. Whether or not that’s true is up for debate, but Dr Popp ended up not standing trial after an assessment of his mental state – so we’ll let you decide.
How damaging is ransomware for businesses?
Now that you’re practically an expert in ransomware, let’s consider why it’s so important to prevent ransomware attacks in your business.
First and foremost, the sheer number of ransomware attacks has increased enormously in the last decade, with a reported 181.5 million ransomware attacks in the first half of 2018 alone.
Remember that, even if a company doesn’t cough up the ransom, such attacks can still cause significant downtime which comes with costs of its own. Plus, even companies who do pay the ransom aren’t guaranteed to have the problem immediately resolved (never trust a criminal, as they say).
Want some hard numbers? A recent report by Sophos has revealed some fascinating statistics about ransomware and its effect on businesses.
Here are some of the key takeaways:
- 94% of businesses which suffered a ransomware attack did get their data back.
- Of those who did get the data back, 56% did so using a backup as opposed to just 26% who paid the ransom.
- 73% of ransomware attacks used the encryption method.
- The cost of managing a ransomware attack is actually doubled for businesses who choose to pay up.
Prevent ransomware (the easy way) with Get Support
As you can see, ransomware can be a big problem for big and small businesses alike. From the stress of having your files inaccessible to the moral dilemma of wondering whether or not you should pay the ransom – it’s a headache most businesses don’t need.
Luckily, the team at Get Support can help.
While conventional antivirus platforms are insufficient to detect and deal with ransomware attacks, the same is not true to Endpoint Detection and Response (EDR) platforms. You can learn a lot more about these in our Plain English guide, but the key point is that EDR systems can a.) help you to detect ransomware before it strikes (e.g. before the trojan is executed), and b.) roll back file changes if they are successful.
If that sort of protection sounds good to you, simply fill in the form below to ask for more details, or call the team anytime on 01865 59 4000.